 |
|
 |
 |
Menu |
 |
|
 Home Home |
| |
|
 Discussions Discussions |
| |
|
 Tools Tools |
| |
|
 Affiliates Affiliates |
| |
|
 Content Content |
| |
|
 Info Info |
| | |
|
|
|
|
 |
User Info |
 |
 Membership: Membership:
 Latest: MichaelSnaRe Latest: MichaelSnaRe
 New Today: 0 New Today: 0
 New Yesterday: 0 New Yesterday: 0
 Overall: 9144 Overall: 9144
 People Online: People Online:
 Visitors: 38 Visitors: 38
 Members: 0 Members: 0
 Total: 38 Total: 38
|
|
|
|
|
 |
Full disclosure |
 |
|
|
 |
|
 |
 |
|
 |
IT Security and Insecurity Portal |
|
 |
All new RainbowCrack 1.4 is out there |
 |
 Posted: Wed Jul 14, 2010 10:27 pm Posted: Wed Jul 14, 2010 10:27 pm |
 |
|
| sEcZx |
| Regular user |

 |
|
| Joined: Jul 09, 2010 |
| Posts: 9 |
|
|
|
 |
 |
 |
|
Focus on more effective rainbow table file format. Features added:
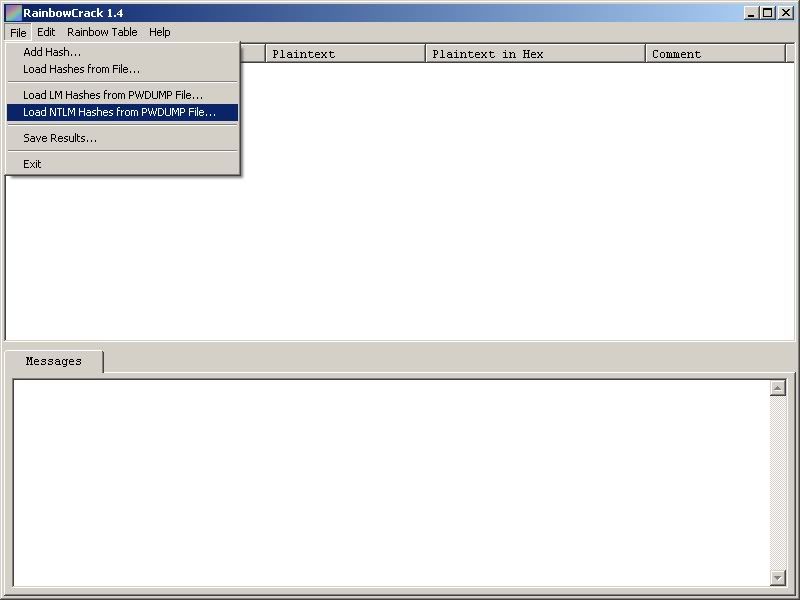
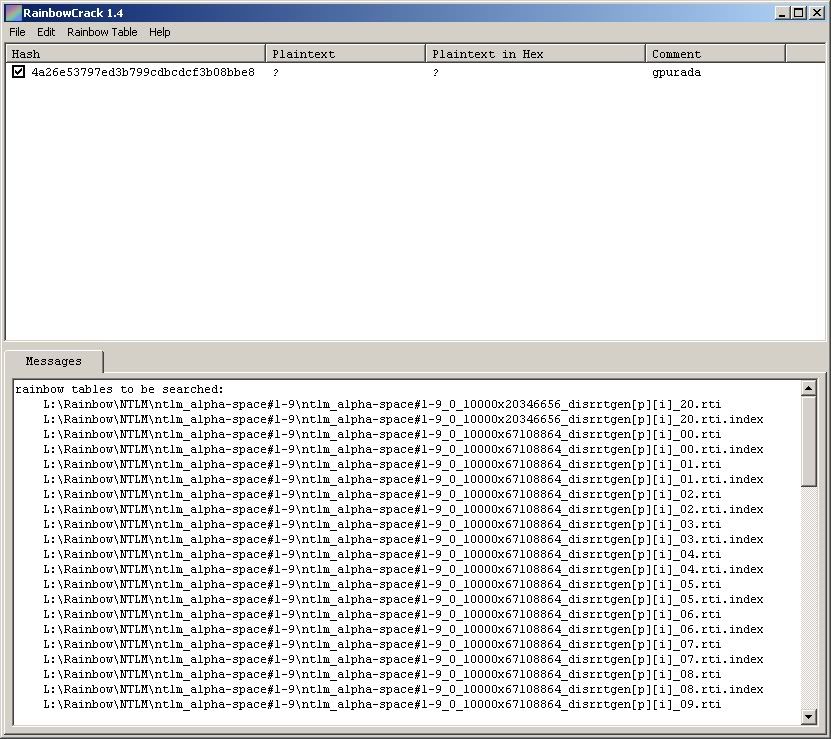
** New compact rainbow table file format (.rtc) reduce rainbow table size by 50% to 56.25%
** New rt2rtc utility convert rainbow table from raw file format (.rt) to compact file format (.rtc)
** New rtc2rt utility convert rainbow table from compact file format (.rtc) to raw file format (.rt)
** The rcrack/rcrack_cuda program support both .rt and .rtc rainbow table file format
** Conversion from non-perfect to perfect rainbow table is supported by rt2rtc utility
>> Some other Features : <<
** Full time-memory tradeoff tool suites, including rainbow table generation, sort, conversion and lookup
** Support rainbow table of any hash algorithm
** Support rainbow table of any charset
** Support rainbow table in raw file format (.rt) and compact file format (.rtc)
** Computation on multi-core processor support
** Computation on GPU (via NVIDIA CUDA technology) support (not freely available)
** Computation on multi-GPU (via NVIDIA CUDA technology) support (not freely available)
** Runs on Windows XP 32-bit and Windows Vista 32-bit
** Command line user interface
>> How RainbowCrack work : <<
RainbowCrack tool is brute force hash cracker generate
It generates all possible plaintexts and compute the corresponding hashes on the fly, and then compare the hashes with the target hash. The plaintext is found if one of them match, otherwise the intermediate computation results are discarded.
Supported Hases
LM, NTLM, MD5, SHA1, MYSQLSHA1, HALFLMCHALL, NTLMCHALL
World Largest MD5 Rainbow Table
recently generated the “md5_ascii-32-95#1-8″ rainbow table.
Table specification:
hash algorithm: md5
charset: space and !”#$%&’()*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\]^_`abcdefghijklmnopqrstuvwxyz{|}~
plaintext length: 1 to 8
key space: 6,704,780,954,517,120 (about 252.5)
table size: 576 GB
With this rainbow table, we can crack md5 hashes of plaintexts up to 8 characters in 30 minutes.
Example hashes crackable by “md5_ascii-32-95#1-8″ rainbow table:
MD5(>4y|DW+B) = 80c94c48024f8e7638d4efb55675ddbc
MD5(Qi)g&F^1) = 1fa7aaa488319b21d541764f3e5bcfff
MD5(lAFd`#~6) = 3af0e600f602a8ecf5149c51b57119da
We have talked about RainbowCrack Here and also compared it with other and found much better specialy combination of GPU and RainbowCrack, It is much faster and better.
Downnload
http://www.project-rainbowcrack.com/rainbowcrack-1.4-win.zip |
|
|
|
|
 |
www.waraxe.us Forum Index -> Tools
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
|
All times are GMT
Page 1 of 1
|
|
|
|
Powered by phpBB © 2001-2008 phpBB Group
|
|
|
|
|
|
|
